Modbus RTU Serial Link Tuning: Baud Rate, Parity, and Timeout Optimization for Reliable PLC Communication [2026]
Modbus TCP gets all the attention in modern IIoT deployments, but Modbus RTU over RS-485 remains the workhorse of industrial communication. Millions of devices — temperature controllers, VFDs, power meters, PLCs, and process instruments — speak Modbus RTU natively. When you're building an edge gateway that bridges these devices to the cloud, getting the serial link parameters right is the difference between rock-solid telemetry and a frustrating stream of timeouts and CRC errors.
This guide covers the six critical parameters that govern Modbus RTU serial communication, the real-world trade-offs behind each one, and the tuning strategies that separate production-grade deployments from lab prototypes.
The Six Parameters That Control Everything
Every Modbus RTU serial connection is defined by six parameters that must match between the master (your gateway) and every slave device on the bus:
1. Baud Rate
The baud rate determines how many bits per second travel across the RS-485 bus. Common values:
| Baud Rate | Bits/sec | Typical Use Case |
|---|---|---|
| 9600 | 9,600 | Legacy devices, long cable runs (>500m) |
| 19200 | 19,200 | Standard industrial default |
| 38400 | 38,400 | Mid-range, common in newer PLCs |
| 57600 | 57,600 | Higher-speed applications |
| 115200 | 115,200 | Short runs, high-frequency polling |
The real-world constraint: Every device on the RS-485 bus must use the same baud rate. If you have a mix of legacy power meters at 9600 baud and newer VFDs at 38400, you need separate RS-485 segments — each with its own serial port on the gateway.
Practical recommendation: Start at 19200 baud. It's universally supported, tolerant of cable lengths up to 1000m, and fast enough for most 1-second polling cycles. Only go higher if your polling budget demands it and your cable runs are short.
2. Parity Bit
Parity provides basic error detection at the frame level:
- Even parity (E): Most common in industrial settings. The parity bit is set so the total number of 1-bits (data + parity) is even.
- Odd parity (O): Less common, but some older devices default to it.
- No parity (N): Removes the parity bit entirely. When using no parity, you typically add a second stop bit to maintain frame timing.
The Modbus RTU specification recommends even parity with one stop bit as the default (8E1). However, many devices ship configured for 8N1 (no parity, one stop bit) or 8N2 (no parity, two stop bits).
Why it matters: A parity mismatch doesn't generate an error message — the slave device simply ignores the malformed frame. You'll see ETIMEDOUT errors on the master side, and the failure mode looks identical to a wiring problem or wrong slave address. This is the single most common misconfiguration in Modbus RTU deployments.
3. Data Bits
Almost universally 8 bits in modern Modbus RTU. Some ancient devices use 7-bit ASCII mode, but if you encounter one in 2026, it's time for a hardware upgrade. Don't waste time debugging 7-bit configurations — the Modbus RTU specification mandates 8 data bits.
4. Stop Bits
Stop bits mark the end of each byte frame:
- 1 stop bit: Standard when using parity (8E1 or 8O1)
- 2 stop bits: Standard when NOT using parity (8N2)
The total frame length should be 11 bits: 1 start + 8 data + 1 parity + 1 stop, OR 1 start + 8 data + 0 parity + 2 stop. This 11-bit frame length matters because the Modbus RTU inter-frame gap (the "silent interval" between messages) is defined as 3.5 character times — and a "character time" is 11 bits at the configured baud rate.
5. Byte Timeout
This is where things get interesting — and where most tuning guides fall short.
The byte timeout (also called "inter-character timeout" or "character timeout") defines how long the master waits between individual bytes within a single response frame. If the gap between any two consecutive bytes exceeds this timeout, the master treats it as a frame boundary.
The Modbus RTU specification says: The inter-character gap must not exceed 1.5 character times. At 9600 baud with 11-bit frames, one character time is 11/9600 = 1.146ms, so the maximum inter-character gap is 1.5 × 1.146ms ≈ 1.72ms.
What actually happens in practice:
At 9600 baud: 1 char = 1.146ms → byte timeout ≈ 2ms (safe margin)
At 19200 baud: 1 char = 0.573ms → byte timeout ≈ 1ms
At 38400 baud: 1 char = 0.286ms → byte timeout ≈ 500μs
At 115200 baud: 1 char = 0.095ms → byte timeout ≈ 200μs
The catch: At baud rates above 19200, the byte timeout drops below 1ms. Most operating systems can't guarantee sub-millisecond timer resolution, especially on embedded Linux or OpenWrt. This is why many Modbus RTU implementations clamp the byte timeout to a minimum of 500μs regardless of baud rate.
Practical recommendation: Set byte timeout to max(500μs, 2 × character_time). On embedded gateways running Linux, use 1000μs (1ms) as a safe floor.
6. Response Timeout
The response timeout defines how long the master waits after sending a request before declaring the slave unresponsive. This is the most impactful tuning parameter for overall system performance.
Factors that affect response time:
- Request transmission time: At 19200 baud, an 8-byte request takes ~4.6ms
- Slave processing time: Varies from 1ms (simple register read) to 50ms+ (complex calculations or EEPROM access)
- Response transmission time: At 19200 baud, a 40-register response (~85 bytes) takes ~48.7ms
- RS-485 transceiver turnaround: 10-50μs
The math for worst case:
Total = request_tx + slave_processing + turnaround + response_tx
= 4.6ms + 50ms + 0.05ms + 48.7ms
≈ 103ms
Practical recommendation: Set response timeout to 200-500ms for most applications. Some slow devices (energy meters doing power quality calculations) may need 1000ms. If you're polling temperature sensors that update once per second, there's no penalty to a generous 500ms timeout.
The retry question: When a timeout occurs, should you retry immediately? In production edge gateways, the answer is nuanced:
- Retry 2-3 times before marking the device as offline
- Insert a 50ms pause between retries to let the bus settle
- Flush the serial buffer between retries to clear any partial frames
- Track consecutive timeouts — if a device fails 3 reads in a row, something has changed (wiring, device failure, address conflict)
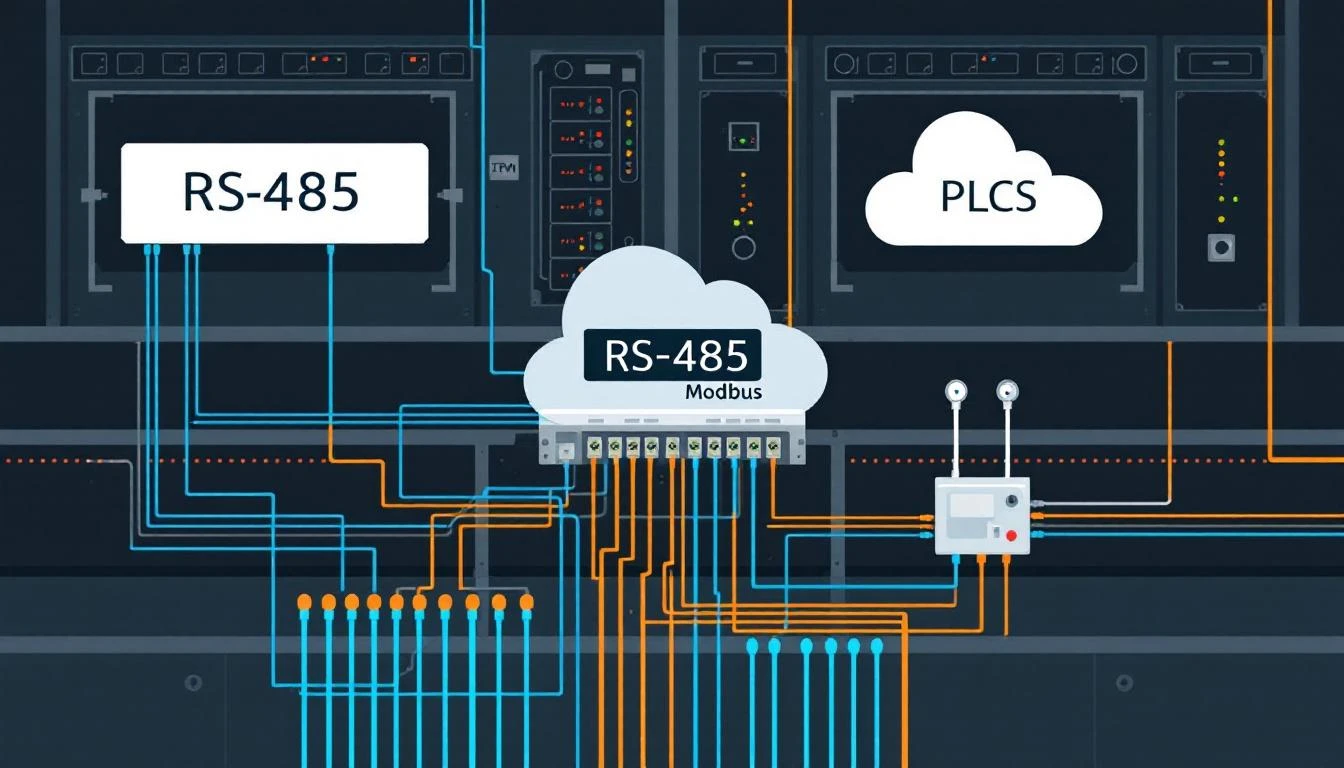
RS-485 Bus Topology: The Physical Foundation
No amount of parameter tuning can compensate for bad RS-485 wiring. The critical rules:
Daisy-chain only. RS-485 is a multi-drop bus, NOT a star topology. Every device must be wired in series — A to A, B to B — from the first device to the last.
Gateway ---[A/B]--- Device1 ---[A/B]--- Device2 ---[A/B]--- Device3
|
120Ω terminator
Termination resistors: Place a 120Ω resistor across A and B at both ends of the bus — at the gateway and at the last device. Without termination, reflections on long cable runs cause bit errors that look like random CRC failures.
Cable length limits:
| Baud Rate | Max Cable Length |
|---|---|
| 9600 | 1200m (3900 ft) |
| 19200 | 1000m (3200 ft) |
| 38400 | 700m (2300 ft) |
| 115200 | 300m (1000 ft) |
Maximum devices per segment: The RS-485 spec allows 32 unit loads per segment. Modern 1/4 unit-load transceivers can push this to 128, but in practice, keep it under 32 devices to maintain signal integrity.
Slave Address Configuration
Every device on a Modbus RTU bus needs a unique slave address (1-247). Address 0 is broadcast-only (no response expected), and addresses 248-255 are reserved.
The slave address is configured at the device level — typically through DIP switches, front-panel menus, or configuration software. The gateway needs to match.
Common mistake: Address 1 is the factory default for almost every Modbus device. If you connect two new devices without changing addresses, neither will respond reliably — they'll both try to drive the bus simultaneously, corrupting each other's responses.
Contiguous Register Grouping: The Bandwidth Multiplier
The most impactful optimization for Modbus RTU polling performance isn't a link parameter — it's how you structure your read requests.
Modbus function codes 03 (Read Holding Registers) and 04 (Read Input Registers) can read up to 125 contiguous registers in a single request. Instead of issuing separate requests for each tag, a well-designed gateway groups tags by:
- Function code — holding registers and input registers require different commands
- Address contiguity — registers must be adjacent (no gaps)
- Polling interval — tags polled at the same rate should be read together
- Maximum PDU size — cap at 50-100 registers per request to avoid overwhelming slow devices
Example: If you need registers 40001, 40002, 40003, 40010, 40011:
- Naive approach: 5 separate read requests (5 × 12ms round-trip = 60ms)
- Grouped approach: Read 40001-40003 in one request, 40010-40011 in another (2 × 12ms = 24ms)
The gap between 40003 and 40010 breaks contiguity, so two requests are optimal. But reading 40001-40011 as one block (11 registers) might be acceptable — the extra 7 "wasted" registers add only ~7ms of transmission time, which is less than the overhead of an additional request-response cycle.
Production-grade gateways build contiguous read groups at startup and maintain them throughout the polling cycle, only splitting groups when address gaps exceed a configurable threshold.
Error Handling: Beyond the CRC
Modbus RTU includes a 16-bit CRC at the end of every frame. If the CRC doesn't match, the frame is discarded. But there are several failure modes beyond CRC errors:
ETIMEDOUT — No response from slave:
- Wrong slave address
- Baud rate or parity mismatch
- Wiring fault (A/B swapped, broken connection)
- Device powered off or in bootloader mode
- Bus contention (two devices with same address)
ECONNRESET — Connection reset:
- On RS-485, this usually means the serial port driver detected a framing error
- Often caused by electrical noise or ground loops
- Add ferrite cores to cables near VFDs and motor drives
EBADF — Bad file descriptor:
- The serial port was disconnected (USB-to-RS485 adapter unplugged)
- Requires closing and reopening the serial connection
EPIPE — Broken pipe:
- Rare on physical serial ports, more common on virtual serial ports or serial-over-TCP bridges
- Indicates the underlying transport has failed
For each of these errors, a robust gateway should:
- Close the Modbus connection and flush all buffers
- Wait a brief cooldown (100-500ms) before attempting reconnection
- Update link state to notify the cloud that the device is offline
- Log the error type for remote diagnostics
Tuning for Specific Device Types
Different industrial devices have different Modbus RTU characteristics:
Temperature Controllers (TCUs)
- Typically use function code 03 (holding registers)
- Response times: 5-15ms
- Recommended timeout: 200ms
- Polling interval: 5-60 seconds (temperatures change slowly)
Variable Frequency Drives (VFDs)
- Often have non-contiguous register maps
- Response times: 10-30ms
- Recommended timeout: 300ms
- Polling interval: 1-5 seconds for speed/current, 60s for configuration
Power/Energy Meters
- Large register blocks (power quality data)
- Response times: 20-100ms (some meters buffer internally)
- Recommended timeout: 500-1000ms
- Polling interval: 1-15 seconds depending on resolution needed
Central Chillers (Multi-Circuit)
- Dozens of input registers per compressor circuit
- Deep register maps spanning 700+ addresses
- Naturally contiguous register layouts within each circuit
- Alarm bit registers should be polled at 1-second intervals with change detection
- Process values (temperatures, pressures) can use 60-second intervals
Putting It All Together
A production Modbus RTU configuration for a typical industrial gateway looks like this:
# Example configuration (generic format)
serial_port: /dev/ttyUSB0
baud_rate: 19200
parity: even # 'E' — matches Modbus spec default
data_bits: 8
stop_bits: 1
slave_address: 1
byte_timeout_ms: 1
response_timeout_ms: 300
# Polling strategy
max_registers_per_read: 50
retry_count: 3
retry_delay_ms: 50
flush_between_retries: true
How machineCDN Handles Modbus RTU
machineCDN's edge gateway handles both Modbus TCP and Modbus RTU through a unified data acquisition layer. The gateway auto-configures serial link parameters from the device profile, groups contiguous registers for optimal bus utilization, implements intelligent retry logic with bus-level error recovery, and bridges Modbus RTU data to cloud-bound MQTT with store-and-forward buffering. Whether your devices speak Modbus RTU at 9600 baud or EtherNet/IP over Gigabit Ethernet, the data arrives in the same normalized format — ready for analytics, alerting, and operational dashboards.
Need to connect legacy Modbus RTU devices to a modern IIoT platform? machineCDN bridges serial protocols to the cloud without replacing your existing equipment. Talk to us about your multi-protocol deployment.